Iris Recognition
STREET-LEVEL SURVEILLANCE
Street-Level Surveillance
Iris Recognition
Iris recognition or iris scanning is the process of using visible and near-infrared light to take a high-contrast photograph of a person’s iris. It is a form of biometric technology in the same category as face recognition and fingerprinting.
Advocates of iris scanning technology claim it allows law enforcement officers to compare iris images of suspects with an existing database of images in order to determine or confirm the subject’s identity. They also state that iris scans are quicker and more reliable than fingerprint scans since it is easier for an individual to obscure or alter their fingers than it is to alter their eyes.
Iris scanning raises significant civil liberties and privacy concerns. It may be possible to scan irises from a distance or even on the move, which means that data could be collected surreptitiously, without individuals’ knowledge, let alone consent. There are security concerns as well: if a database of biometric information is stolen or compromised, it is not possible to get a new set of eyes like one would get a reissued credit card number. And iris biometrics are often collected and stored by third-party vendors, which greatly expands this security problem.
How Iris Recognition Works
Iris scanning measures the unique patterns in irises, the colored circles in people’s eyes. Biometric iris recognition scanners work by illuminating the iris with invisible infrared light to pick up unique patterns that are not visible to the naked eye. Iris scanners detect and exclude eyelashes, eyelids, and specular reflections that typically block parts of the iris. The final result is a set of pixels containing only the iris. Next, the pattern of the eye’s lines and colors are analyzed to extract a bit pattern that encodes the information in the iris. This bit pattern is digitized and compared to stored templates in a database for verification (one-to-one template matching) or identification (one-to-many template matching).
What Kinds of Data Are Collected for Iris Recognition
Iris scanners collect around 240 biometric features, the amalgamation of which are unique to every eye. The scanners then create a digital representation of that data. That numeric representation of information extracted from the iris image is stored in a computer database.
Who Sells Iris Recognition Technology
How Law Enforcement Uses Iris Recognition
The New York City Police Department was among the first police departments to begin using iris recognition. The department installed BI2 Technologies’ mobile MORIS (Mobile Offender Recognition and Information System) in the fall of 2010. Although New York City’s use of iris scanning in jails was supposed to be voluntary, there have been reports of arrestees being held longer for declining iris photographs. Prisons, such as the Rhode Island Department of Corrections, have also begun using the technology. An EFF survey of California law enforcement agencies in 2015 found that sheriff offices in Orange County and Los Angeles County had plans to implement iris scanning technology.
The B12 database is housed by a third-party vendor in an undisclosed location in San Antonio, Texas, and in three other disaster backup facilities. A BI2 executive told The Intercept that it is the largest database of its kind in North America.
Threats Posed by Iris Recognition
Perhaps the biggest threat of iris scanning is the danger of a national database that can track people covertly, at a distance or in motion, without their knowledge or consent. This raises significant civil liberties and privacy concerns which increase as iris data are collected from more and more people. It may be possible for law enforcement officers to use long-range iris scanners on people simply glancing in their rear view mirror after being pulled over. At some point, it’s possible that every person could be identified at any place, even if they are not suspected of committing a crime.
There also are grave concerns with local law enforcement sharing biometric data to help federal immigration agencies such as the U.S. Immigration and Customs Enforcement (ICE), which has direct access to many law enforcement databases.
It is also possible to trick or bypass iris scanners. In 2012, security researchers at the Universidad Autonoma de Madrid were able to recreate images of irises from digital codes stored in security databases. More recently, hackers with the Chaos Computer Club in Germany were able to bypass the iris-based authentication in Samsung’s Galaxy S8 smartphone (despite the company’s claims of “airtight security,”) by simply taking a digital photograph of the owner’s face in night shot mode, printing it out, superimposing a contact lens on the image, and holding the image in front of the locked phone.
And then there is the issue of data security. It’s unclear what steps, if any, law enforcement agencies are taking to secure the sensitive biometric data they collect. Databases of iris biometric are a honeypot of sensitive, highly personal data that will be targeted by criminals. Data breaches and hacks are at an all-time high. Biometric information is a special risk because it’s not possible to revoke, cancel, or reissue an eyeball if digital biometric information is stolen or compromised. Making the risk of data breach even greater, law enforcement often stores its iris biometrics on databases operated by vendors and other private third parties. This also gives companies access to and control over criminal justice data, which many of their employees can access remotely.
For More Information
Most recently updated October 25, 2019
Iris Recognition Technology
Iris Recognition Technology
Iris recognition is the best of breed authentication process available today. While many mistake it for retinal scanning, iris recognition simply involves taking a picture of the iris; this picture is used solely for authentication. But what makes iris recognition the authentication system of choice?
Traditional Notions of Establishing Identity
Historically, identity or authentication conventions were based on things one possessed (a key, a passport, or identity credential), or something one knew (a password, the answer to a question, or a PIN.) This possession or knowledge was generally all that was required to confirm identity or confer privileges. However, these conventions could be compromised – as possession of a token or the requisite knowledge by the wrong individual could, and still does, lead to security breaches.
The Emergence of Biometrics
To bind identity more closely to an individual and appropriate authorization, a new identity convention is becoming more prevalent. Based not on what a person has or knows, but instead on what physical characteristics or personal behavior traits they exhibit, these are known as biometrics – measurements of behavioral or physical attributes – how an individual smells, walks, signs their name, or even types on a keyboard, their voice, fingers, facial structure, vein patterns or patterns in the iris.
Biometric Appeal of Iris Recognition
Of all the biometric technologies used for human authentication today, it is generally conceded that iris recognition is the most accurate. Coupling this high confidence authentication with factors like outlier group size, speed, usage/human factors, platform versatility and flexibility for use in identification or verification modes – as well as addressing issues like database size/management and privacy concerns – iris recognition has also shown itself to be exceedingly versatile and suited for large population applications.
Other System Components
IrisAccess system incorporates other system-designed elements. A low profile Identity Controller (ICU) offers easy greater integration convenience while ensuring that biometric templates are kept safe, protected and secure, off the imager.
The Biology Behind the Technology
The Advantage of Iris Recognition
Iris recognition is an attractive technology for identity authentication for several reasons.
75 Years of Innovation: Iris recognition
The ability to use iris recognition in real-life scenarios by removing previous constraints
The 75 Years of Innovation series highlights the groundbreaking innovations spanning from SRI’s founding in 1946 to today. Each week, SRI will release an innovation, leading up to its 75th anniversary in November 2021.
In a blink of an eye: How SRI captured your Iris On the Move (IOM)
When you look into someone’s eyes what do you see? I wager you say the iris, that circle of color in the human eye that is so engaging. The iris plays a crucial role in our sight. If you shine a light into an eye, the muscles that are part of the iris contract. If you walk into a darkened room, the iris muscles expand to allow more light in to help you see.
An iris has another special feature. Like a fingerprint, an iris presents a unique pattern. This allows the iris to be used as a biometric providing a way to uniquely identify a person. In 2006, Sarnoff Corporation (now part of SRI International) developed an innovation in iris recognition that would make the technique much more commercially viable.
Here, the spotlight is placed on the Iris on the Move® (IOM) technology.
Opening the eyes of the world to iris recognition on the move
Iris recognition was not a new discipline when Sarnoff developed its “Iris on the Move®” (IOM) technology. As early as the 1930s, ophthalmologist Frank Burch suggested that an iris could be used in the identification of an individual. In 1995, the first commercial products using iris recognition became available. These were based on patented algorithms by J.G. Daugman.
However, iris recognition, at that point, had some serious constraints. Earlier systems required an individual to be in a fixed position and placed at a specific angle, close enough to capture the iris image. In other words, the capture of the unique pattern of a given iris was dependent on the individual being static. These constraints were not caused by the iris recognition algorithms, rather the image capture itself restricted the capabilities of the technology. They also presented commercial issues in the types of use cases iris recognition could be used for.
This latter issue in image capture — requiring a user to be in a fixed position and close to the camera — became a focus for researchers at Sarnoff Corporation; Dr. Matey and his research team at Sarnoff, led the efforts to resolve this. This team went on to develop an image capture system that used high-resolution cameras, video synchronized strobed illumination and specularity based image segmentation.
An iris recognition system that was on the move
Iris recognition technology is an accurate and secure method of identifying an individual. The assurance that the recognition of an individual is correct is higher than that of a fingerprint, for example. The problem with biometric factors, such as with fingerprints, is that fingerprint scanners rely on contact and can quickly become dirty, requiring regular maintenance. Whereas eyes are ‘self-cleaning’, and iris scanners can work at a reasonable distance. Other factors in creating commercially viable biometric identification systems include ease of use, ease of deployment and cost.
But older iris scanners, as mentioned, had the dual constraints of fixed position and close distance: These iris scanners could not be used for people who were walking or if a person was at a far distance. It was the use of iris recognition in real-world scenarios that Sarnoff worked to resolve. The IOM system was in prototype by 2006. In 2008, Sarnoff demoed its “Drive-Through and new Compact Iris on the Move® (IOM)” iris capture system at the Biometric Consortium Conference in Florida. In 2009, the IOM system was tested out at Schiphol airport in the Netherlands. The IOM system was able to verify individuals by scanning irises from a distance as they moved through security checks. The IOM system was shown to identify individuals at speeds of up to 30 people per minute.
IOM in the palm of your hand
Since then, the Iris on the Move® (IOM) system has found major success. Commercial products based on the IOM technology include the IOM PassPort SL used for corporate lobbies and airports. In 2013, the Iris on the Move (IOM) PassThru system was shown to handle drive-up scenarios that were outdoors and in all lighting conditions. Drivers did not need to remove gloves, headgear, glasses or contact lenses and could remain in their car. In 2014, Samsung chose Iris on the Move technology as the access control mechanism in their mobile devices.
In 2016, SRI spun-out a company, Princeton Identity Inc., to take the IOM technology and develop it further. Since then, the IOM technology has been applied to sports venues, medical and healthcare applications as well as for border control across the world. In 2018, Princeton Identity’s solution, Access500e™, was deployed at Dubai International Airport, the system being able to process travelers within one to two seconds, providing security without affecting the overall travel experience.
Iris recognition, like many of the inventions borne of the SRI International stable, has been made into a commercially viable technology by taking advantage of SRI’s and associates’ expertise. Sarnoff Corp’s deep knowledge of image capture and high-resolution camera technology provided the necessary capability to take iris recognition algorithms and create innovations that work in real-life situations.
Interested to see more from SRI? Visit sri.com.
J. G. Daugman, “High confidence visual recognition of persons by a test of statistical independence,” in IEEE Transactions on Pattern Analysis and Machine Intelligence, vol. 15, no. 11, pp. 1148–1161, Nov. 1993, doi: 10.1109/34.244676.
Understanding about IRIS Recognition Technology
In the 1980’s, two ophthalmologists Aran Safir and Dr Leonard Flom proposed that no two irises are similar, even in twins, thus making them good biometric authentication units. This concept was based on the clinical experience with which they viewed the individual features of irises such as crypts, coronas, colors, pits, contraction furrows, striations, freckles and rifts. After researching and documenting the use of irises as a means of recognizing people, they were awarded a copyright in 1987. In 1990, Dr. John Daugman created the algorithm to implement iris technology. These algorithms utilize the methods of some mathematical calculations and pattern recognition of iris.
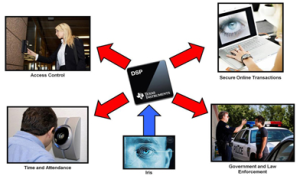
Nowadays access control systems are becoming more essential. The number of systems that have been compromised is ever increasing and one area where security can be enhanced is authentication. A biometric and Iris technology afford secure methods of identification and authentication. Iris Technology is used in many areas like airport security, ATMs, physical access security and information security.
Iris Recognition Technology
Iris-recognition is a biometric technology which deals with the recognition based on the human Iris. Iris-recognition technology is considered to be the most accurate biometric technology available today. The Iris is an inner organ of the body which is observable, or it is the area of the eye wherein the colored or pigmented circle, which is generally blue or brown, rings the dark purple area of the eye.
Iris Recognition System
Iris feature is an easy option of a person to prove his identity, which is based on his biometrics at any time and at any place. Iris recognition is an important identifying approach in many departments such as finance, navigation, etc. This system’s main features include Iris capturing, Image quality evaluation, Iris region segmentation, feature extraction, similarity calculation and decision making. Every part is very important in this recognition system for correct recognition of a person’s identity.
There are plenty of features in iris areas of human eye’s image. The iris is a small and black object, and capturing of iris image is not an easy work. To capture iris, we have to maintain some distance about 4 to 13 cm under a good-lighting environment. For many evident image recognition systems, infrared light source is better such as face-recognition system. It can perform a better light for enhancing image contrast, and furthermore, infrared light is harmless to eyes. In order to capture the best iris image, a person’s cooperation is necessary, and also the captured image supports iris recognition. A good cooperation can reduce the capacity of iris pre- processing and make iris recognition a real-time character. Therefore, under incorporate conditions so many researchers initiate to study the theory of imperfect iris recognition.
The process and working of iris recognition takes place like this: a picture of the iris is captured by a camera attached to a wall within a distance of 4 to 13 inches, and then the image is processed by a special type of software that separates the main iris patterns from the inner and outer boundaries of the iris. By using Dr. Daugman’s algorithm, the patterns of the iris from the processed image are encoded into a 512-bit code called as the iris code. The encoded code is encrypted as soon as it is calculated to avoid from theft. The calculated iris code is then compared to the codes that are stored in the database for matching and pattern recognition. The speed of searching the database can be up to10,000 codes/sec. Therefore, within a few seconds, a person can be recognized without any particular user action.
Iris Scanner
Iris Scanners are becoming more and more common in security applications nowadays as no two people’s eyes share similar iris patterns, and thus they are less matchable. Iris scanning has become very advanced, but at the heart of the system is a CCD digital camera. This camera uses both infrared and visible light to take a clear picture of a person’s iris. When a person’s pupil is black – with near IR light – to isolate the iris and pupil is easier for the computer. When a person looks into an iris scanner, the digital camera automatically focuses audible feedback from the system to make the person’s position correctly. When the camera takes a picture from 3 to 10 inches distance, the computer locates the center of the pupil, edge of the iris and pupil, the eye lashes and eyelids. It then calculates the patterns of the iris and translates them into a code.
The iris is a visible but protected structure, and it doesn’t change over a time usually. Most of the time a person’s eyes also stay unchanged even after eye surgery and even blind people can use these scanners as long as their eyes have irises. Typically contact lenses and eye glasses do not cause inaccurate readings.
Biometric System
Nowadays a biometric access control system plays an essential role, and this system has realized the value of biometrics for two reasons: one is to identify, and the other to verify. The benefit of using biometric authentication is that it cannot be forgotten or lost as the person needs to be available during the point of identification process. Essentially, this system is more capable and reliable than the token-based and traditional knowledge-based techniques.

A Biometric system is a technological system that uses information about a person to identify that person. In order to work effectively, these systems depend on particular data based on some exclusive biological traits and qualities. This system has its major hub in distributions of electronic security system such as access-control system, time-attendance system based on fingerprints, facial-recognition attendance system, smartcard and proximity-based products, etc. The characteristic of biometrics can be classified into two types, which is represented in the following figure.
Physiological Biometrics: These types of biometric systems are related to the shape of the body and these systems include face recognition, iris recognition, fingerprint recognition, hand recognition and DNA recognition.
Behavioral Biometrics: These types of biometric systems are related to the behavior of a person and this type of biometrics includes voice, keystroke and signature recognition.
Advantages
Disadvantages
Applications
Thus, Iris technology has proved to be a very useful and adaptable security measure. It is an accurate and quick way of identifying an individual with no chance of human error. Iris recognition is widely used in many applications where security is necessary. In the future it will prove to be a widely used security measure.
Photo Credits:
iris recognition
1 iris recognition
2 iris recognition
3 iris recognition
4 iris recognition
5 iris scanner
См. также в других словарях:
iris recognition — or iris scanning noun A security system which uses a digital camera to detect the unique marks on a person s iris and map these to information on a database in order to confirm the person s identity • • • Main Entry: ↑iris … Useful english dictionary
Iris recognition — Infobox Anatomy Name = Iris Latin = Caption = The iris is the green/grey/brown area. The other structures visible are the pupil in the centre and the white sclera surrounding the iris. The overlying cornea is pictured, but not visible, as it is… … Wikipedia
iris recognition — /ˈaɪrəs rɛkəgnɪʃən/ (say uyruhs rekuhgnishuhn) noun the process of identifying a person by analysing the unique pattern of their iris and matching it against an existing record … Australian-English dictionary
Iris Recognition Immigration System — (IRIS) is an initiative to provide automated clearance through UK immigration for certain frequent travellers. IRIS relies on biometric technology to authenticate identity and is part of the e borders initiative of the UK… … Wikipedia
IRIS — can refer to: In technology * IRIS T, a German air to air missile * International Reactor Innovative and Secure, an advanced light water nuclear reactor design * Internal Rotary Inspection System, an ultrasonic method for the nondestructive… … Wikipedia
Recognition (disambiguation) — Recognition is identification of something already known or acknowledgement of something as valid. The term may have the following specialized meanings.*Recognition (sociology), an acknowledgement of merits. *Recognition (diplomacy), acceptance… … Wikipedia
Iris-Erkennung — Iriserkennung mit einem Handgerät Die Iriserkennung ist eine Methode der Biometrie zum Zweck der Authentifizierung oder Identifizierung von Personen. Dafür werden mit speziellen Kameras Bilder der Iris (Regenbogenhaut) des Auges aufgenommen, mit… … Deutsch Wikipedia
Iris-Scan — Iriserkennung mit einem Handgerät Die Iriserkennung ist eine Methode der Biometrie zum Zweck der Authentifizierung oder Identifizierung von Personen. Dafür werden mit speziellen Kameras Bilder der Iris (Regenbogenhaut) des Auges aufgenommen, mit… … Deutsch Wikipedia
iris scanning — noun biometric identification by scanning the iris of the eye the structure of the iris is very distinctive • Hypernyms: ↑biometric identification, ↑biometric authentication, ↑identity verification * * * iris recognition or iris scanning noun A… … Useful english dictionary