Citrix StoreFront “Cannot complete your request”
Encountered an error on Citrix StoreFront 3.0 today regarding authentication.
All users received the well known error “Cannot complete your request” upon login.
Event Log on StoreFront-server showed errors with ID 10:
“A CitrixAGBasic Login request has failed.
Citrix.DeliveryServicesClients.Authentication.AG.AGAuthenticatorException, Citrix.DeliveryServicesClients.Authentication, Version=3.0.0.0, Culture=neutral, PublicKeyToken=null
Authenticate encountered an exception.
at Citrix.DeliveryServicesClients.Authentication.AG.AGAuthenticator.Authenticate(HttpRequestBase clientRequest, Boolean& passwordSupplied)
at Citrix.Web.AuthControllers.Controllers.GatewayAuthController.Login()”
and ID 2:
“Access is denied. Contact your system administrator.
System.ServiceModel.EndpointNotFoundException, System.ServiceModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
There was no endpoint listening at net.pipe://localhost/Citrix/Authentication/Win32 that could accept the message. This is often caused by an incorrect address or SOAP action. See InnerException, if present, for more details.”
Turns out the service called “Citrix Default Domain Services” had actually stopped. Next time I will definitely check the running services before starting troubleshooting on IIS and Citrix Netscaler.
Published by torivar
2 Replies to “Citrix StoreFront “Cannot complete your request””
Thank you, labored a lot before I found this post. Installation had configured the Citrix Default Domain Services as Automatic Delay so service was never started, changed it to automatic and started the service on the Store Front server and it works.
Leave a Reply Cancel reply
This site uses Akismet to reduce spam. Learn how your comment data is processed.
Issue: “Cannot Complete Your Request” Error after Citrix ADC 13.0 b64.35 Upgrade
Issue and Background
Yesterday, Citrix released a security bulletin outlining several “Low” and “Medium” risk vulnerabilities as covered in CTX281474 and outlines the firmware versions available for download which mitigate those vulnerabilities.
Included in the Citrix ADC 13.0 build 64.35 release are additional security enhancements to SSO to block by default weaker authentication methods for SSO. The supporting documentation located here, outlines basic authentication, digest authentication, and NTLM without the Negotiate NTLM2 key or negotiate sign as the affected “weaker” methods impacted, whilst other methods such as SAML, Kerberos, OAuth and form-based authentication are supposedly unaffected. As of September 18th, 2020 at least, those documented statements may not be entirely accurate.
Testing reveals that SSO functionality is broken when attempting to access Citrix StoreFront through Citrix Gateway and an error of “Cannot complete your request” appears when using SAML. The Citrix Gateway configuration tested against is purely SAML so this came as a surprise, albeit it is possibly an interaction issue with IIS. Citrix has noted this behaviour in CTX281592 and points back to the Citrix Docs on the subject of SSO enhancements. This doc does cover how to override the default security measures in the new firmware build using traffic policies bound to the Citrix Gateway vServer.
It is possible that this security enhancement may make its way into other builds such as 12.x so this guidance may become valid for more than 13.0 in the future.
In this article, we’ll walk through how to quickly fix the issue and restore a Citrix Gateway to service.
Resolution
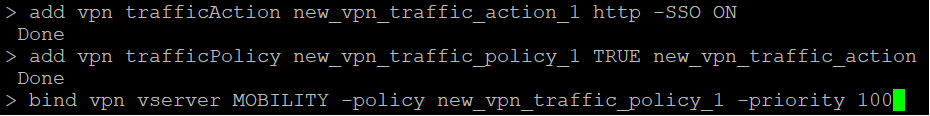
Step 1
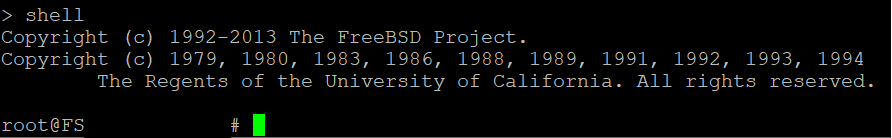
SSH into the ADC appliance and enter into shell mode.
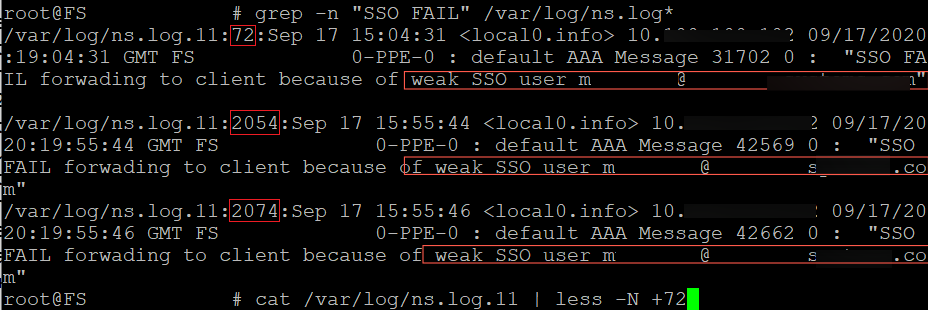
The syslog message generated we are looking for is “SSO FAIL forwarding to client because of weak SSO user user@email.com”. To quicken this process grep through the cleartext ns.log with:
If this does not produce any hits, the logs might have been rotated in which you can use the zgrep command
The output shows the filename : line_number : content of the line.
We have 3 matches from my failed attempts so to investigate further, we’ll follow line number 72, 2054 and 2074 of the file ns.log.11. The cat command will be used or alternatively the zcat for gzip compressed logs. Vi can also be used as an alternative.
(type q to quit after investigating)
Step 2
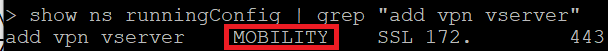
Now that we have confirmation SSO is the cause of this issue, type exit to enter the ADC command line interface. A new vpn policy will need to be attached so let’s find out the name of the currently added vpn vservers.
Step 3
A new traffic action and policy will need to be added. Copy and paste the following 3 commands changing with the vserver name found in the command above.
Step 4
At this point, re-test authentication to Citrix Gateway and confirm SSO passthrough works. Be sure to save your config!
Terence Luk
Tackling the daily challenges of technology. one project at a time.
Pages
Monday, April 21, 2014
Launching Citrix XenDesktop 7.x StoreFront Receiver Web website throws the error: “Cannot complete your request.”
Problem
You attempt to access the Citrix XenDesktop 7.x StoreFront Receiver Web website directly but receive the following error:
Cannot complete your request
Log On

Solution
One of the reasons why you would receive this error is if you have a mismatch between your Citrix StoreFront’s Base URL and the URL you are accessing the website with your browser:

Note that the Base URL configured in the StoreFront is http://zencont01srv/ while the browser URL used to access the website was http://zenstore01.srv. To correct the problem, change the base URL to match the URL you are using to access the website in the browser.
4 comments:
nice blog dear friend
wishes for long time blogging
I’m new to citrix
please can u upload posts about citrix cloud platform & cloud portal/bridge
Thanks a lot. Although I know that incorrect base url can cause this issue, but at the time of my issue, I did not check carefully. After reading your post, I decided to recheck my base url and found that two characters are swapped and changing this fixed my issue.
Nice one. Thanks Mate for the useful blog.
I would also like you all to know that this issue can also come up when SQL database connection has exceeded its limits.
Error: “Cannot Complete Your Request” When Connecting to StoreFront
Where to Start Troubleshooting
In order to identify what steps need to be followed when troubleshooting the error, you will have to identify where the issue is occurring by performing the following 3 tests:
Do you get the error when connecting directly to the StoreFront server? If yes, start troubleshooting from step 1.
Perform this test by adding the StoreFront base URL and the StoreFront server local IP address to the Hosts file of the internal machine you will be testing with. For more information about editing the Hosts file refer to the following article – How to use a Hosts file to test a site that uses host headers on an Intranet.
Do you get the error connecting through a load balancer? If yes, start troubleshooting from step 13.
From the testing machine open the command prompt and ping the StoreFront base URL FQDN. The FQDN should resolve to the IP address of your load balancer. If it does not then verify your DNS settings or the Hosts file on the local machine.
Do you get the error only when connecting through your NetScaler Gateway? If yes, start troubleshooting from step 19.
From the testing machine open the command prompt and ping the NetScaler Gateway FQDN. The FQDN should resolve to the IP address of your NetScaler Gateway. If it does not then verify your DNS settings or the Hosts file on the local machine.
Troubleshooting Steps
Troubleshooting the Storefront Server Connection
Note: StoreFront 3.x has the loopback feature, for configuration guidance refer to Citrix Blog – What’s New in StoreFront 3.0.
Make sure that the certificate on the StoreFront server is not expired.
Make sure the “Certificate Issued To” name matches the StoreFront base URL.The certificate should also contain a private key. If using a SAN certificate, make sure the StoreFront Base URL is listed under the subject alternative names. Wildcard certificates are also supported.
View the Certification Path tab on the certificate and confirm that all the Intermediate and Root certificates are properly installed in order to complete an SSL Handshake. For more information regarding certificates see article – Server Certificates.
Troubleshooting the Load Balancer
Troubleshooting NetScaler Gateway
Open the StoreFront MMC > NetScaler Gateway > Select the Gateway you configured > Change General Settings > NetScaler Gateway URL and confirm external users are using the same URL for external access on the browser and Citrix Receiver.
On the StoreFront server open the Command Prompt > Ping NetScaler Gateway FQDN and confirm it resolves to the correct gateway IP address.
On the StoreFront server open a browser and navigate to the NetScaler Gateway URL to confirm there are no certificate errors. For more information refer to article CTX128539 – How to Link an Intermediate Certificate to the Server Certificate on NetScaler/NetScaler Gateway.
Open the StoreFront MMC and go to NetScaler Gateway > select the gateway you are configuring > Change General Settings > Subnet IP address and remove it. The subnet IP address is only needed if you are using a NetScaler 9.x firmware or under certain use cases concerning GSLB as mentioned here. Specifying the VIP of a NetScaler Gateway (not SNIP) may be required if the StoreFront implementation supports multiple NetScaler Gateways with the same URL (such as the same URL being used internally and externally, but resolving to different NetScaler Gateways) along with unique callback URLs. That being said, only certain use cases and the use of NetScaler 9.x firmware necessitate populating the Subnet IP address field which should otherwise be left blank.
On the same Change General Settings window from step 22, confirm the Logon Type is set to Domain if using LDAP authentication on the NetScaler Gateway. For more information to Citrix Documentation – Configure NetScaler Gateway connection settings.
On the same Change General Settings window from step 22, confirm the Callback URL FQDN listed resolves to the NetScaler Gateway VIP by using the ping command on the Command Prompt from the StoreFront server. Once you verify it resolves to the correct gateway IP address, open a browser on the StoreFront server and navigate to it and confirm there are no certificate errors.
On the NetScaler Gateway VIP go to Authentication > LDAP Policy > Edit Server and confirm the following settings:
For more information refer to – User authentication.
Go to the Session Policy bound to the NetScaler Gateway VIP > Edit Profile > Client Experience > Single Sign-on to Web Applications and confirm that it is checked. Then go to the Published Applications tab > Single Sign-on Domain and confirm the correct domain is specified.
Note: For domain users in a multi-domain environment, add the SSO Name Attribute field as UserPrincipalName under LDAP Policy configuration and uncheck the Single Sign-on Domain for the authentication on the session profile.
Check the NetScaler Gateway VIP > SSL Parameters > TLSv1 and confirm that it is enabled. StoreFront 3.0.1 or prior does not support TLS 1.1 and TLS 1.2. Make sure the Callback VIP has TLS 1.0 enabled.
On the NetScaler Gateway VIP verify the “No Rewrite Clientless” policy on the NetScaler Gateway VIP is configured to use the expression TRUE.
On the NetScaler go to Security > Application Firewall and confirm the feature is disabled. If it is enabled bypass the policies during testing. If successful re-enable the Application Firewall in learning mode,so it can Learn and Allow the necessary StoreFront traffic. For more information refer to article CTX117003 – How to Configure Learning Parameters on the Application Firewall.
Other Scenarios
If you only get the error when accessing the server for first time after an idle time or running an antivirus scan then disable the File Change Notification feature on the IIS server where StoreFront is running.
Find app bitness from appPool advance settings.
64 bit: To enable this hotfix, you must add the following DWORD value of 1 at the following registry key:
32 bit: If you are running a 32-bit process on an x64-based system, add the following DWORD value of 1 at the following registry key:
For more information refer to the following blogs:
Is there an error in the Event Viewer for “An unexpected error occurred storing the credentials” (Event ID 8) or “An error occurred during authentication” (Event ID 3)?
If so, run the following PowerShell command:
cd ‘C:Program FilesCitrixReceiver StoreFrontScripts’
$certlist = @(Get-DSCertificate)[0] | where
And then restart the Citrix Credential Wallet Service.
If any timeout settings have been modified manually through the web.config file located under C:inetpubwwwrootCitrixAuthenticationweb.config then make sure the SessionState timeout field is set to the default value of 5.
If using Microsoft NLB as a load balancer; it has been reported that using Microsoft “NLB” type load balancing with unicast mode might trigger this issue. Switching to multicast mode helps resolve this issue.
When a single FQDN configuration is used then refer to the following Citrix Documentation to verify if any step is skipped or misconfigured – Create a single Fully Qualified Domain Name (FQDN) to access a store internally and externally. You can potentially get the cannot complete request error.
If you were configuring Optimal Gateway for launching applications, make sure the configuration on the web.config file has a proper closing HTML tag. For more information regarding Optimal Gateway configuration then refer to Citrix Documentation – Configure optimal NetScaler Gateway routing for a store.
If you experience the error after publishing a new application or customizing an application’s icon, check the event viewer on the StoreFront server and look for the following errors:
Event 1 = There was an error during a resources List request. System.Net.WebException, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
The remote server returned an error: (500) Internal Server Error.
Event 7 = Unhandled exception thrown for route “DazzleResources/List” System.ArgumentException, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089 Offset and length were out of bounds for the array or count is greater than the number of elements from index to the end of the source collection.
The workaround is to go to Studio > Delivery Groups > Applications > view the properties of the application recently added > Delivery > Application Icon > Change and choose from any of the Citrix default icons.
If you received this error during implementation of ADFS, Azure and FAS then consider the following – SAML authentication does not use a password and only uses the user name. Also, SAML authentication only informs users when authentication succeeds. If SAML authentication fails, users are not notified. Since a failure response is not sent, SAML has to be either the last policy in the cascade or the only policy.
So when you configure SAML authentication along with LDAP authentication on NetScaler, use the following guidelines – if SAML is the primary authentication type, then disable authentication in the LDAP policy and configure it for group extraction. Now, bind the LDAP policy as the secondary authentication type.
If this error occurs after an upgrade, then go to IIS > Default Site > StorenameWeb > Default Files > delete default.html and recreate default.html file manually.
Disable self-recycling for the following application pools:
Citrix delivery services authentication
Citrix delivery services resources
Citrix receiver for web
Verify if all the required network is reachable from NetScaler Gateway. Routing table should also look complete.
Examine the logs on NetScaler Gateway to verify if it is blocking any cookies, in case expression for cookie header is used in the session policy.
If the issue occurs specially after an HA failover of NetScaler Gateway, then verify the time on both the nodes. The time on nodes should be in sync. Examine the ntpd process and sync the time if the nodes are not in sync.
Error: “Cannot complete your request” in StoreFront
When accessing a store website on StoreFront, the following error message is displayed:
“Cannot complete your request. You can log on and try again, or contact your help desk for assistance.”
Important! This article is intended for use by System Administrators. If you are experiencing this issue and you are not a System Administrator, contact your organization’s Help Desk for assistance.
Note: The first troubleshooting step should be to review?? the messages in the Event Viewer of StoreFront, and the local computer account running the Receiver which displays “Cannot complete your request”. The errors in the Event Viewer logs?? will provide you guidance?? on where to start investigating the behavior in the sections listed in?? this article.
The article is divided into the following sections:
1.Verify if the StoreFront server can resolve the StoreFront FQDN by pinging the FQDN from the command prompt.
Configure the StoreFront Service to point to itself in a load balanced environment. For additional information, refer to Citrix Documentation – Load balancing with NetScaler.
In a single-server deployment, the Server Base URL must resolve to the StoreFront’s server local IP address.
2.Verify if the StoreFront IIS server is bound?? to 443 and is configured with a certificate?? corresponding to the FQDN.
3.Verify if the common name of the certificate binding in IIS matches the StoreFront’s base URL. If the certificate does not match, issue a new certificate to reflect the StoreFront URL or change the StoreFront URL to match the certificate. After performing the adjustments, run iisreset.
4.If accessing the server externally, validate the callback URL is configured correctly on the StoreFront Server. The behavior can occur?? when the callback URL resolves to the wrong IP or the entered NetScaler Gateway FQDN does not match the certificate on the NetScaler Gateway.
5.Verify that?? the server certificate?? and any intermediate certificate are?? installed on NetScaler Gateway and StoreFront server.
6.If the same FQDN is used on both the NetScaler Gateway and StoreFront, refer to?? Citrix Documentation – Create a single Fully Qualified Domain Name (FQDN) to access a store internally and externally.
7.Verify if a third party tool has made changes to IIS on StoreFront server, such as Windows Updates. Within a specific situation, the error appeared on IIS after a Windows Update:
“Details: CertEnroll::CX509Enrollment::p_InstallResponse: ASN1 bad tag value met. 0x8009310b (ASN:276)”
In this example, the resolution was?? to uninstall and reinstall the certificate on the IIS server.
8.Verify if any legacy sites were upgraded to the latest version of StoreFront. In this example. an entry was found in the web.config file under?? “C:\inetpub\wwwroot\Citrix\Authentication”?? for the “component Backup the web.config file and remove?? the entry.
1.Verify if the “User name and password” authentication method is enabled on the StoreFront server.
2.Verify if the Base URL is configured with an FQDN “example.com” instead of NetBIOS “example”.
4.Verify if users do not have different names in Active Directory. For?? example. the user principal name (UPN)?? name1@domain does not match the pre-Windows 2000 naming?? convention “down-level logon”?? domain\ABCname1.
Adjust the down-level logon to?? match the UPN. For the example, the down-level logon would show in the user profile as?? domain\name1. For additional information, refer to?? User Name Formats.
NetScaler Gateway Authentication
1.Verify if the Single Sign-on?? (SSO) Domain is configured correctly on the NetScaler Gateway.
2.Verify if there is an SSO domain mismatch on NetScaler Gateway and StoreFront.
3.NetScaler Gateway SSO might not be passing the correct information due to incorrect configuration. Verify that the following attributes are configured:
Server Logon Name Attribute: samAccountName
Group Attribute: MemberOf
Sub Attribute Name: CN
SSO Name Attribute: samAccountName
Security Type: PlainText
Note. When LDAP is configured as userPrincipalName, confirm that the SSO Name Attribute field shows the value sAMAccountName when using StoreFront with NetScaler or NetScaler Gateway. Refer to Citrix Documentation – User authentication for more information.
3.Verify the “No Rewrite Clientless” policy on the NetScaler Gateway is configured to use the expression TRUE.
4.In the event log on StoreFront server, the following error is displayed: “CitrixAGBasic single sign-on failed because the credentials failed verification with reason FailedPasswordComplexity”.
In this example, a?? network trace on NetScaler shows the following:
Inside the POST, the credentials are shown.
A blank password field causes the failure. For client certificate to successfully log on to NetScaler Gateway two?? factor authentication. LDAP should be set as the primary. Also, LDAP is required to be set to the primary in the session policy credential index.
5.For domain users in a multi-domain environment, add the SSO Name Attribute field as UserPrincipalName under LDAP configuration and uncheck the Single Sign-on Domain for the authentication.
1.Verify the configuration for?? Method and Persistence in the Load Balancer Virtual Server section within the NetScaler:
Set LoadBalancing Method?? to LEASTCONNECTION
Set Persistence to COOKIEINSERT
For additional information, refer to the Citrix Documentation – Load balancing with NetScaler.
2.Verify if the Load Balancer can resolve the base URL of StoreFront when one of the StoreFront Server is taken offline.
3.If XML servers are load balanced, ensure that X-FORWARDED-FOR is configured for XML LoadBalanced vip.
1.Verify if?? antivirus firewall is installed on the StoreFront server. Disable antivirus firewall and test the connection. Exclude the StoreFront ports within the antivirus firewall. Refer to CTX101810 – Communication Ports Used by Citrix Technologies for the list of StoreFront ports.
2.If McAfee Enterprise antivirus protection is enabled on the StoreFront server, random user will see the error message “Cannot complete your request”. Typically, the first user account will always?? see this error. Add the IIS process W3WP.exe to McAfee exclusion list and restart the server.
3.Verify if NetScaler is using Application Firewall. Test the configuration by disabling the Application Firewall. If successful re-enable the Application Firewall in learning mode. it can Learn and Allow the necessary StoreFront traffic.
4.If a proxy server is configured on the network, verify that the URL?? for proxy is set correctly within the browser LAN settings for Use automatic configuration script setting.
1.Verify the Credential Wallet service is not started or in hung state.
Ensure that the Citrix Credential Wallet Service is set for a Delayed Start and started on the StoreFront server. Restart the Citrix Credential Wallet Service.
2.The Credential Wallet component of StoreFront can prevent users from storing securely used password. When the password cannot be stored using the Credential Wallet, the authentication process cannot complete. Restart the Credential Wallet service on the affected server to restore the functionality. In certain situation, the behavior can reoccur. To permanently resolve the issue, Citrix recommends upgrading to the latest StoreFront.
3.Citrix recommends allowing at least an additional 2 GB of RAM dedicated to StoreFront. The memory allocated to StoreFront will be above the requirements for the operating system and applications installed on the server. Refer to Citrix Blog – StoreFront Scalability Update for additional information.
4.Verify if the Event Viewer has the following error:
Event ID 7: Unhandled exception thrown for route “ExplicitFormsAuthentication/AuthenticateStart” System.Configuration.ConfigurationErrorsException, System.Configuration, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a The Forms Template Engine could not be found in the service locator. at Citrix.DeliveryServices.Authentication.Explicit.FormsCommon.Conversations.ExplicitConversationEngine.CreateConversationState(RequestToken requestToken, ITokenService tokenIssuingService) at Citrix.DeliveryServices.Authentication.FormsProtocol.Conversations.ConversationEngine.StartConversation(RequestToken requestToken, ITokenService tokenIssuingService)
Update the system environment variable directory to C:\Temp instead of D:\Temp.
5.It has been reported that using Microsoft “NLB” type load balancing with unicast mode might trigger this issue. Switching to multicast mode helps resolve this issue.
6.Delete the subnet IP address from StoreFront NetScaler Gateway configuration when internally browsing StoreFront site.